Connects decision-makers and solutions creators to what's next in quantum computing
The researchers found that even the most advanced quantum computers in the world today cannot crack public key encryption.
January 25, 2023
Fujitsu has successfully tested RSA, the widely used cryptosystem for securing public data transmission, for potential vulnerability to code-cracking by quantum computers. The test aimed to see if security concerns about quantum computing posing a threat to currently used cryptographic techniques were valid.
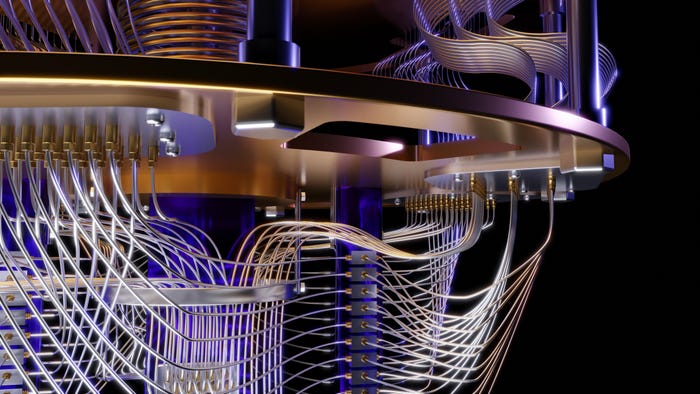
Fujitsu used a 39-qubit quantum simulator to evaluate the resources needed for quantum computers to break existing RSA cryptography. They did this using Shor's algorithm, a method that could break public key cryptography with sufficiently powerful quantum computers.
The researchers found that even the most advanced quantum computers in the world today cannot crack RSA.
A fault-tolerant quantum computer with a scale of around 10,000 qubits and 2.23 trillion quantum gates is needed. Even with this, researchers estimated that it would take about 104 days of fault-tolerant quantum computation to break the RSA encryption successfully.
For reference, IBM recently unveiled its most powerful quantum computer to date, the 433 Qubit Osprey processor.
Fujitsu plans to conduct future assessments of increasingly powerful quantum computers on cryptography security. It will also evaluate the need for quantum-resistant cryptography, even though current research excludes the possibility of quantum computing becoming a threat in the short term.
"Our research demonstrates that quantum computing doesn't pose an immediate threat to existing cryptographic methods,” said Fujitsu senior director of data and security research Tetsuya Izu.
“We cannot be complacent either, however. The world needs to begin preparing now for the possibility that one day quantum computers could fundamentally transform the way we think about security."
Fujitsu plans to increase the performance of its quantum simulator to 40 qubits by the first quarter of fiscal 2023. The company also plans to build a 64-qubit superconducting quantum computer with the assistance of Riken in fiscal 2023.
About the Author(s)
You May Also Like