Connects decision-makers and solutions creators to what's next in quantum computing
US Cyber and Infrastructure Security Agency warns of post-quantum cryptography risk to critical infrastructure

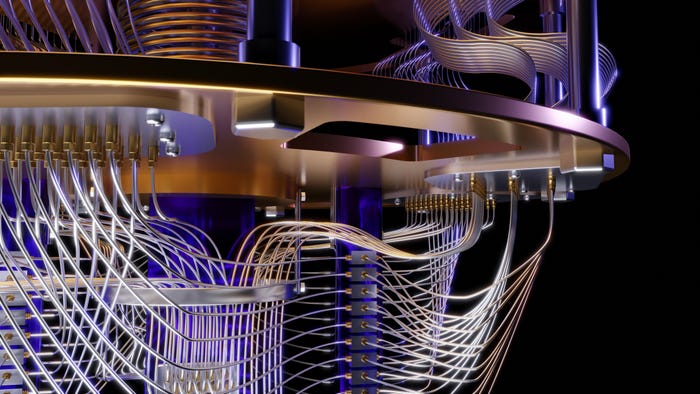
The advent of practical quantum computing threatens the security of even the most securely encrypted information that critical infrastructure depends on.
At the Quantum Computing Summit in Austin, Texas, last week, Florence Lewine, a risk analyst at the U.S. Department of Homeland Security’s Cyber and Infrastructure Security Agency (CISA), told attendees how the government advises organizations to prepare.
CISA leads the U.S. effort on defending critical infrastructure, working with the private sector and government at national and local levels to secure against evolving cyber threats. Within that, the National Risk Management Center (NRMC) provides strategic risk analysis to the critical infrastructure community.
Lewine said the threat will be posed by future “cryptographically-relevant quantum computers,” which will be capable of breaking the asymmetric encryption used today.
“Quantum computing threatens the security of asymmetrically-encrypted information and potentially allows information that was previously believed to be secure to be corrupted or even stolen,” said Lewine. “The exact arrival time of this kind of quantum computer isn't known just yet, but we do know that the threat to information that's protected by asymmetric encryption already exists.”
This is a problem because asymmetric encryption is used widely throughout federal government at state and local levels to secure U.S. critical infrastructure. The threat posed by quantum computers may lead to asymmetric encryption becoming obsolete. The current government effort to protect against it focuses on introducing post-quantum cryptography (PQC) standards.
“These new standards are cryptographic systems that are secure and resistant to both quantum computers and traditionally developed computers and we want standards that can interoperate with both existing protocols and networks,” said Lewine.
“The National Institute of Standards and Technology (NIST) is currently working to finalize these new post-quantum cryptographic standards and expects to publish them in 2024, but preparatory work for that can happen today.”
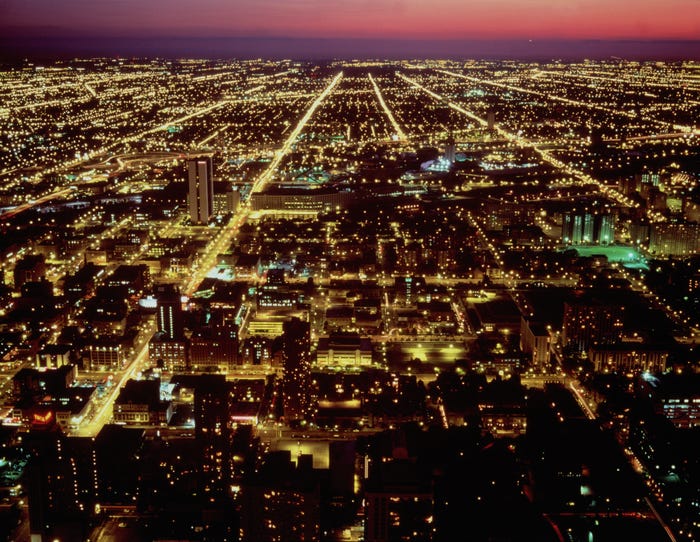
CISA’s risk analysis process focuses on 55 national critical functions (NCF), functions of government that are so vital to the U.S. that their disruption, corruption, or dysfunction would have a debilitating effect on national security. These include clinical communication, distribution methods that allow for the movement of goods and services, national security and public health and the supply of materials that secure the economy.
CISA has identified the NCFs that will enable cascading migration to PQC to ensure that information is kept secure, but Lewine said there are challenges implementing it.
“The first is that NCFs have long-term data confidentiality concerns that are going to be uniquely vulnerable and require additional support,” Lewine said. “Another identified vulnerability is NCFs that are dependent on industrial control systems because of the geographic diversity and the high costs that are associated with upgrading them.”
One of the reasons that these NCFs were assessed to be at risk is because of the “harvest now, decrypt later” threat, whereby an adversary or a nation-state might already be collecting asymmetrically encrypted information intending to break it with a cryptographically relevant quantum computer when available. Organizations that protect national security data, personal health information or any other form of Personal Identifying Information (PII) are especially vulnerable to this type of attack.
“We want to stress that organizations that are dependent on NCFs or operational technology (OT) systems should ensure that hardware replacement cycles are not delayed or skipped and that stakeholders prioritize efforts to migrate to post-quantum cryptography as soon as it's available,” advises Lewine.
Lewine offered advice on what organizations can do now to prepare for post-quantum.
“The main goal is to start planning now,” she said. “If you've learned anything from this conference it is that quantum is coming sooner than you think. And it's important that you do it as owners and operators can find out where vulnerable algorithms lie within your system and your network, and what that data relies on these vulnerable algorithms that you need to protect.”
CISA advises ensuring a full inventory of critical systems to get an understanding of which may rely on vulnerable algorithms and what critical data sits on those systems. Organizations should also check with their vendors to make sure that they're acting on post-quantum. Finally, post-quantum cryptography standards should be integrated into industry-specific standards bodies.
“We understand that this process of adapting to PQC is going to be a multi-year endeavor and we know that it's going to require using both classical computing and quantum-safe implementations for at least several years,” said Lewine.
“The last thing is to work with us as CISA is going to continue to work with the private sector and public sector experts pushing out advisories and updates as we can.”
About the Author(s)
You May Also Like
.png?width=100&auto=webp&quality=80&disable=upscale)
.png?width=400&auto=webp&quality=80&disable=upscale)